Applying Enterprise Integration Patterns in SAP ABAP
In this article, I will attempt to make sense of how for apply Venture Combination Examples in ABAP. Applying Enterprise Integration Patterns in SAP ABAP. Try not to be frightened with the modern term. When you wrap up perusing this page you would acknowledge it is the hello fi name given to the arrangement of examples messages coming to Drain. . So kindly accompany me.
Gregor, H & Woolf, B. (2003), “Learning the technology, however, is just the first step—the real goal is to learn how to effectively apply the technology”.
Starting around 2001 in my whole expert vocation I worked in Microsoft Advancements. Yet, in 2013 the organization I work began a change venture and I got the rare chance to begin as an ABAP engineer I took the courses and did my confirmation. I was prepared in Microsoft regions however I was as yet a novice at SAP ERP world and my most memorable test was to fix an occurrence that was a high need for the organization.
The issue was that the message exchanges at SAP POS DM (Retail location Information The executives) were copying. The issue happened when the source framework for outer reasons re-sent a bunch of messages, in outcome, copying exchanges which could be envisioned in the POSDM Workbench (T-Code/POSDW/MON0) and the effect for the business was that the administration division couldn’t accommodate the marketing projections of the day. Let’s get started with Applying Enterprise Integration Patterns in SAP ABAP.

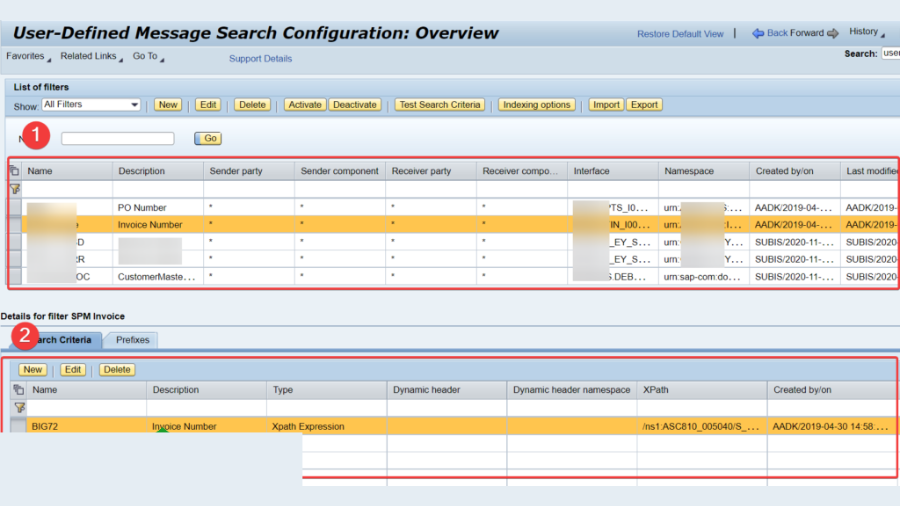
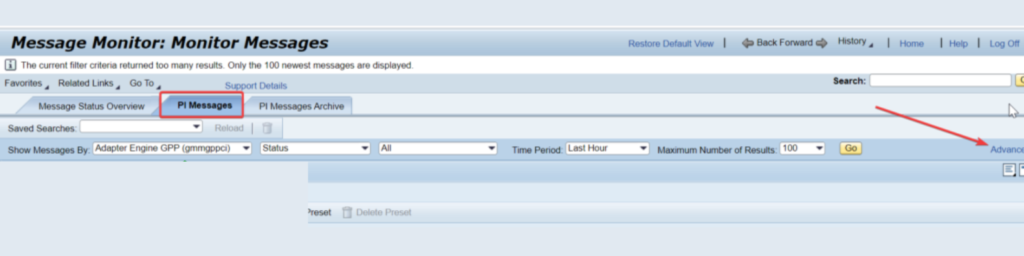
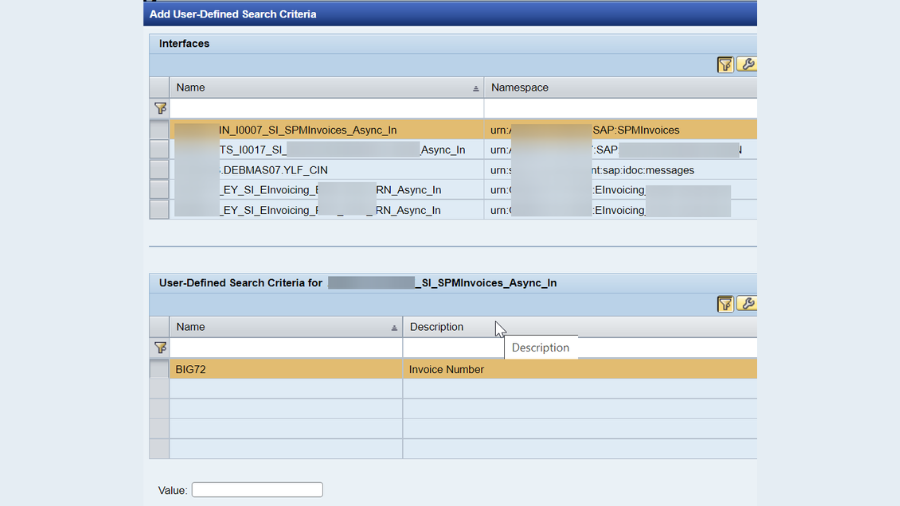
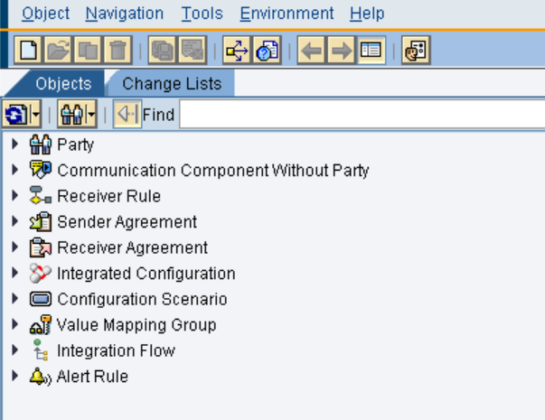
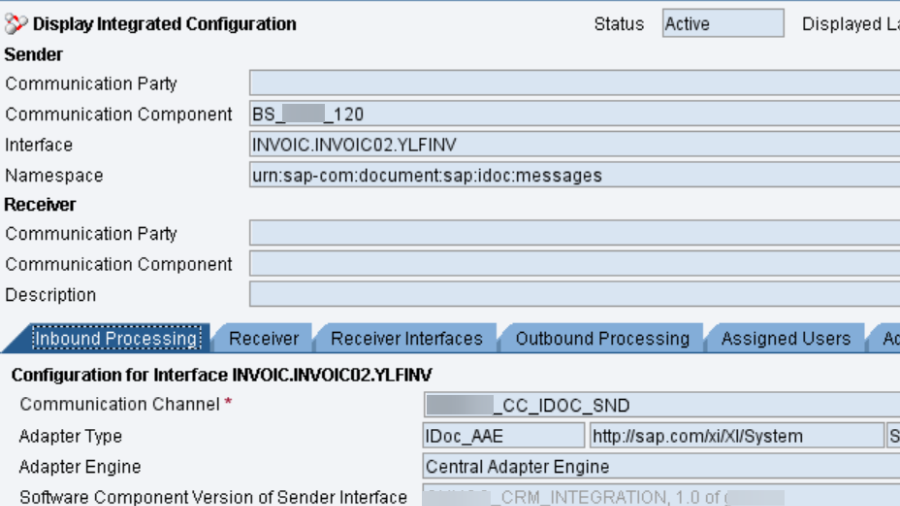
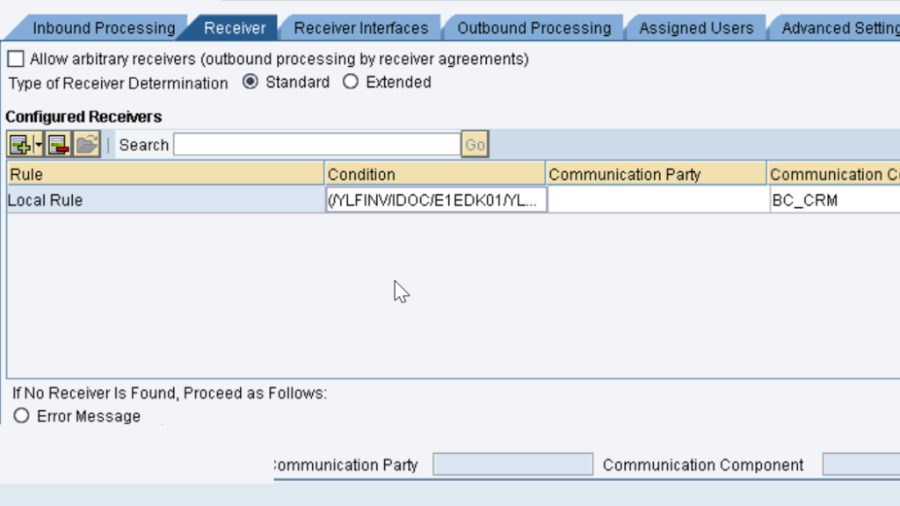
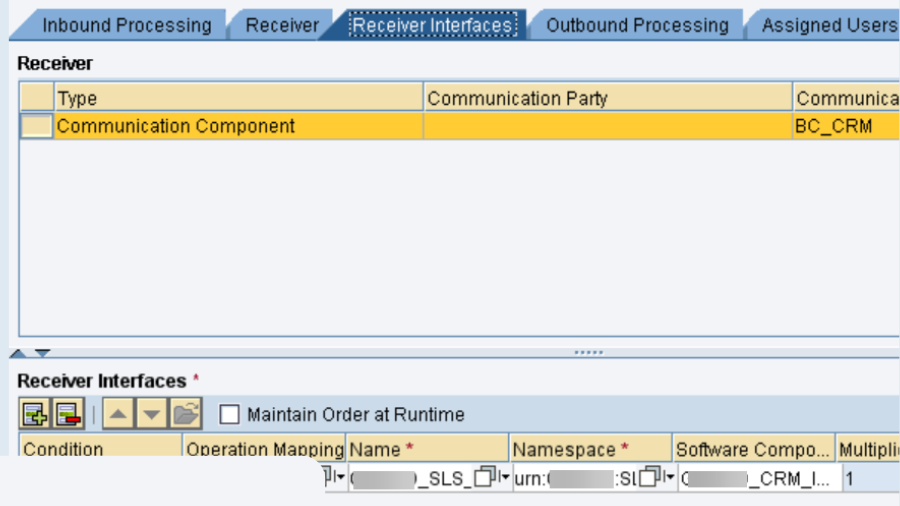
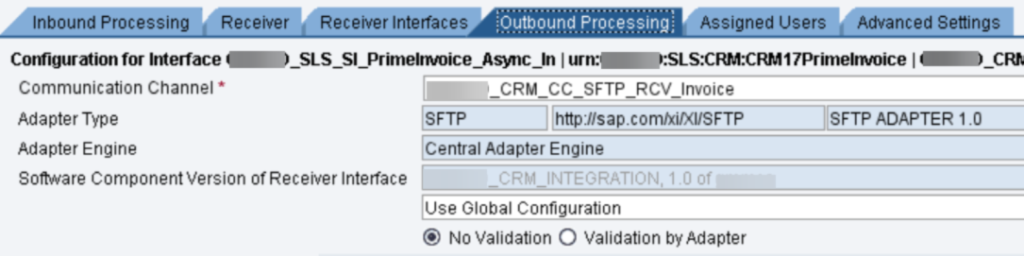
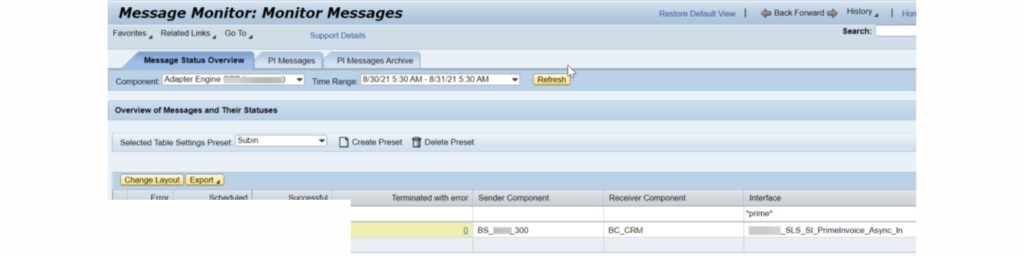
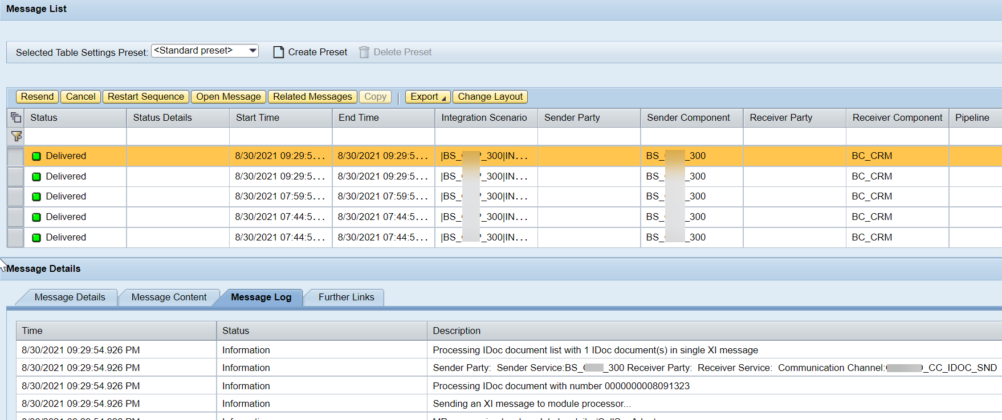
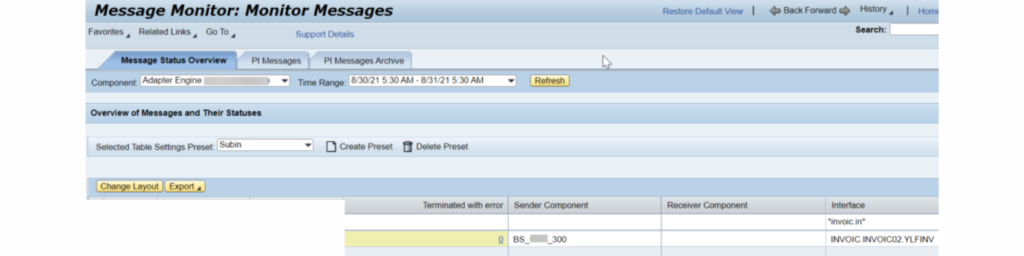
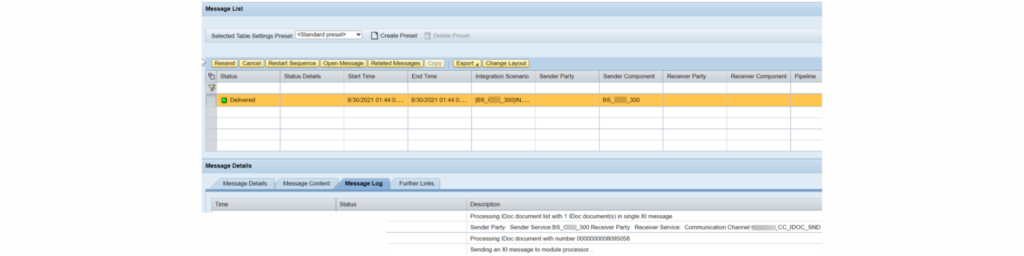
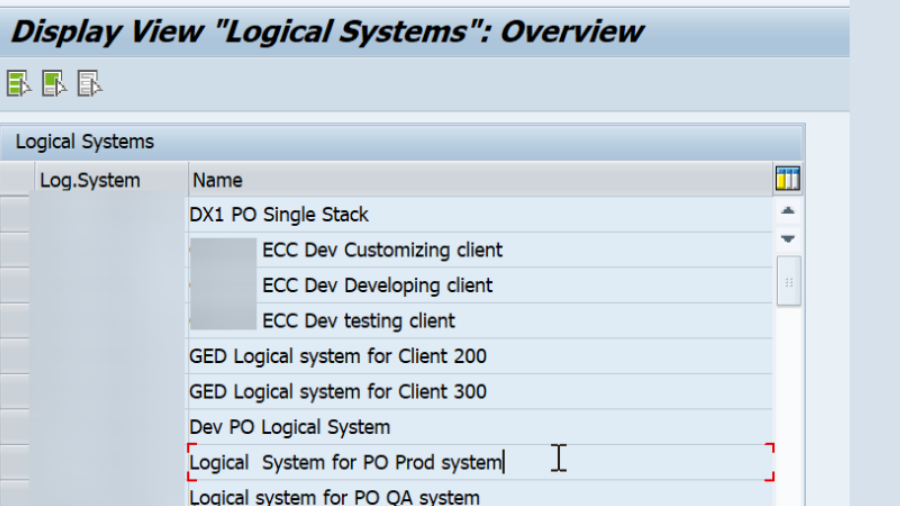
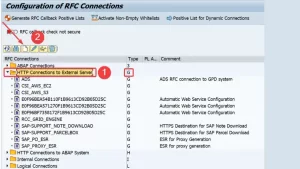
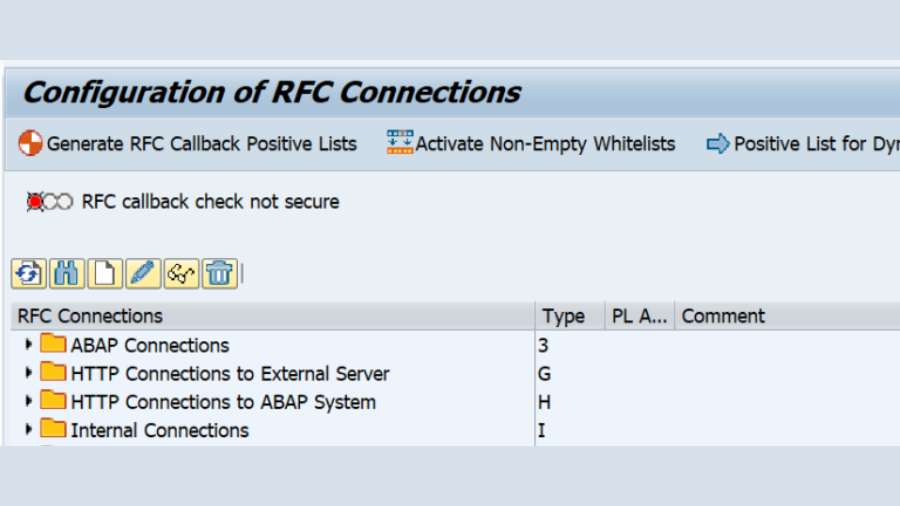
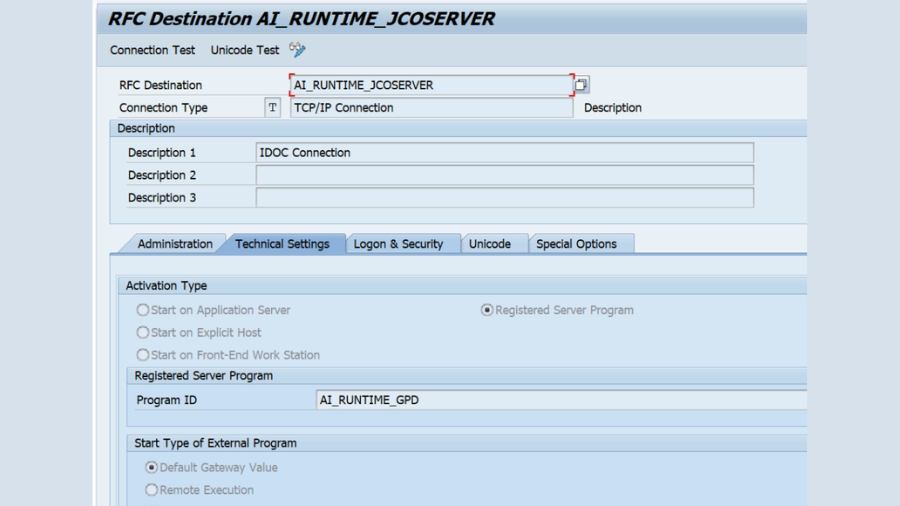
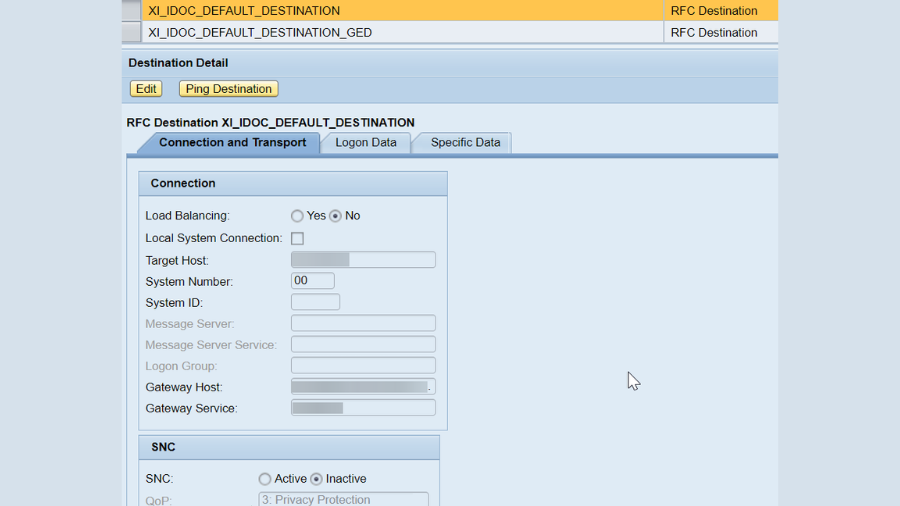
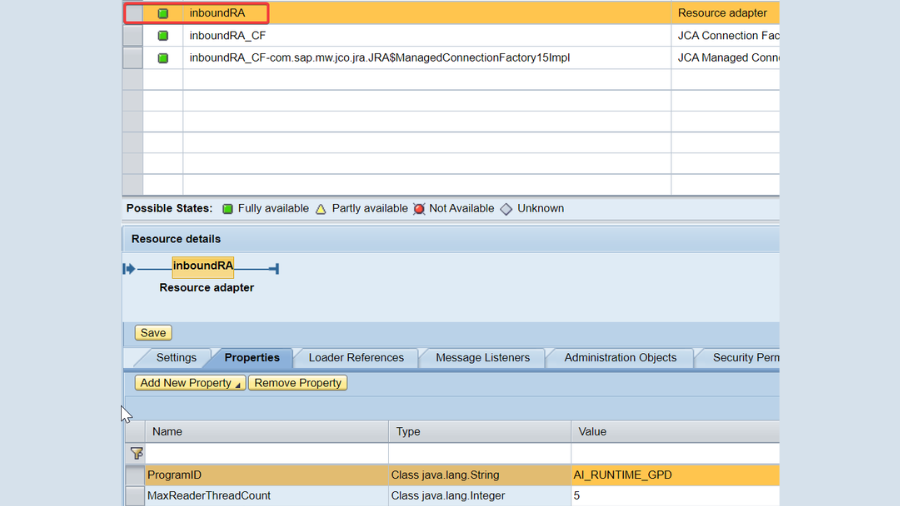
SAP POSDM expected that on occasion you would have a few exchanges copied on the grounds that it needs to resend the directive (for some business need) however only a couple of exemptions, not many copy messages consistently. So according to the perspective of joining, we can hand-off in the shipper so every message of each and every nonconcurrent connection point ought to carry out the Idempotent Collector (one that can securely get similar message on various occasions) combination design. This, obviously, was not yet carried out at the message transport administration. For our situation, the shipper was SAP PI and the collector arrangement was a RFC connector direct call that doesn’t uphold the nature of administration.
The Idempotent Collector design settle how a message beneficiary arrangements with copy messages. Another option could be at the administrations layer, for example, web administration, a solid message that could ensure Nuclear message exchange (for example a bunch of unmistakable changes as a solitary activity) however that sounds another post. Today we would see how we carried out Idempotent Example in the beneficiary connection point in SAP ABAP utilizing Venture Mix Examples.
An improvement or a custom ABAP program Idempotency as per Gregor, H and Woolf, B. (2003) can be accomplished through two essential means:
- Explicit “de-duping“, i.e. the removal of duplicate messages.
- Defining the message semantics to support Idempotency.
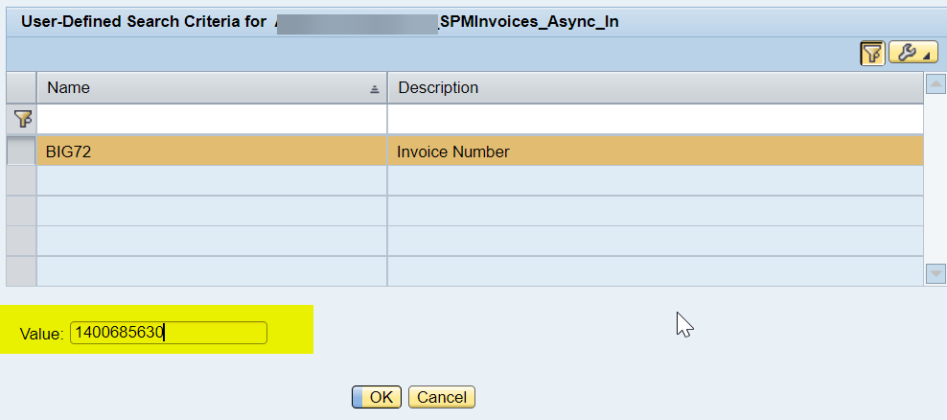
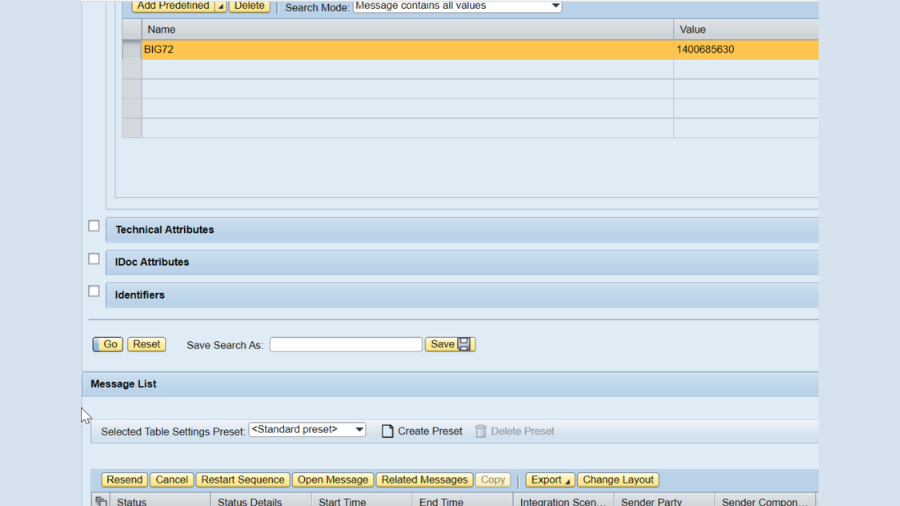
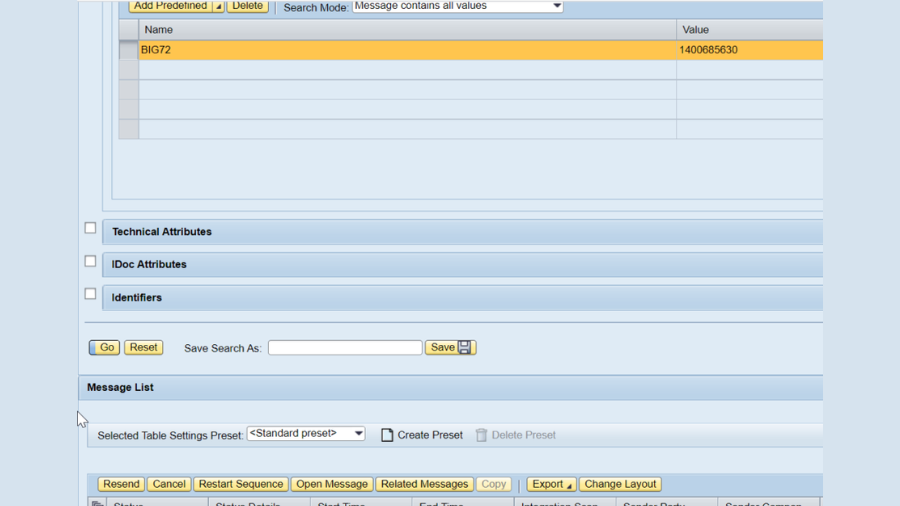
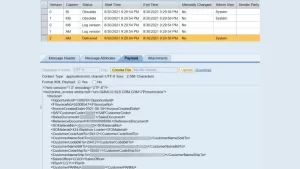
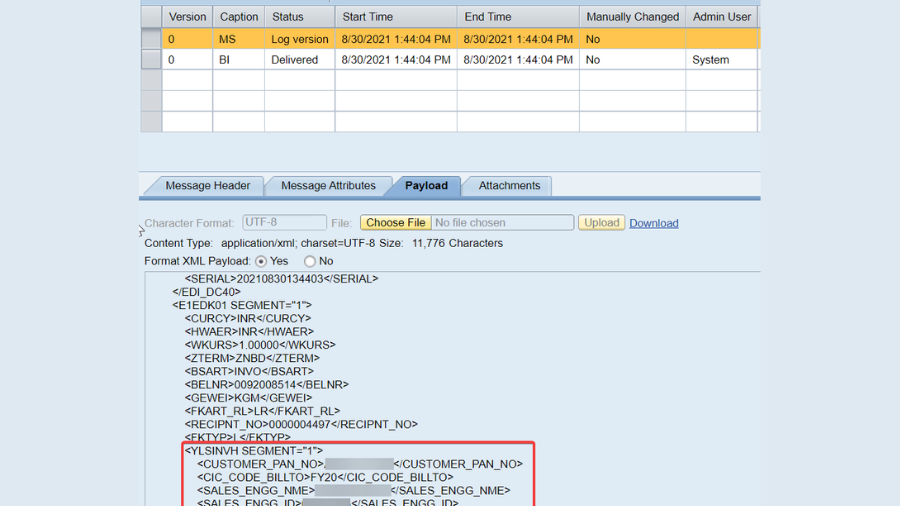
For our situation, e chose to utilize choice number one by monitoring messages that it previously got with the assistance of a special message identifier. For this we recognized the Remote Capability Module (RFC) that was utilized in the message stream to send messages from PI to Drain. The valued RFC was/POSDW/CREATE_TRANSACTIONS_EXT. We were searching for a choice to improve it and fortunate, at the absolute starting point of the capability we found and upgrade point. So without a second thought we carried out the upgrade direct segment toward meet our necessity.

Our plan approach was basic at this point viable thinking about the need of great importance. We made a straightforward table for recording the messages got with a remarkable key utilizing the GUID (Worldwide Extraordinary Identifier). This GUID was important for the approaching boundaries of the capability and it is sent and created by SAP PI for each message. The second field FECMOVTO was the timestamp that we utilized for documenting.

When we made the table we executed the example. There was no such thing as in the event that the approaching message in the table then it would be endured else it would be disposed of. Basic and sweet. Isn’t it?

As per Gregor, H and Woolf, B. (2003), an exceptional message identifier improves on this errand and recognizes those situations where two genuine messages with a similar message content show up. By utilizing a different field, the message identifier, we don’t attach the semantics of a copy message to the message content.

There was one more worry for our IT Planner group. That is, shouldn’t something be said about the table size? With time old records ought to be filed. For this, we composed a straightforward erasure program utilizing the time stamp saved in the table.

This program gets the complete number of records characterized in the info boundaries and erase from the table for information before the date demonstrated in the choice screen.

Keep in mind, I was a fresher to Drain ERP and SAP ABAP. This was my most memorable task as an ABAPer. However, a terrifying one. Be that as it may, a few standards hold great across innovations. As far as I might be concerned, knowing how to involve designs gave me the arrangements in ABAP (even absent a lot of involvement). What’s more, I could choose to utilize this example again in future in some other new stages too. Simply the language structure changes, the engineer’s brain plans/creates in similar way across stages. Isn’t it?
YOU MAY BE INTERESTED IN
SAP HANA Consultant Cost, Fees, And Job
Oracle Coherence: Turbocharging Data Caching for Enhanced Performance